We offers comprehensive Penetration Testing Services, designed to rigorously assess and fortify your organization’s cyber security posture.
Through simulated cyber attacks modeled after the latest hacking techniques, our team of certified experts identifies vulnerabilities in your systems, networks, and applications before they can be exploited by malicious actors.
Common Web Attacks and Our Remediation Strategies
SQL Injection
Attackers exploit vulnerabilities in your database to manipulate queries and access sensitive data. We identify these vulnerabilities through comprehensive testing and mitigate them by implementing prepared statements, parameterized queries, and regular security audits of database operations.
Cross-Site Scripting (XSS)
This attack injects malicious scripts into webpages viewed by users. Our team prevents XSS by employing content security policies, validating and sanitizing user input, and encoding data output.
Cross-Site Request Forgery (CSRF)
CSRF tricks a user into executing unwanted actions on a web application in which they’re authenticated. We safeguard against CSRF attacks by implementing anti-CSRF tokens and ensuring that state-changing requests are protected by proper validation tokens.
Phishing Attacks
Phishing attempts to acquire sensitive information through deception. We combat phishing by conducting regular security awareness training, implementing email filtering solutions, and using multi-factor authentication (MFA) to add an extra layer of security for accessing sensitive information.
Why Choose TDR Networks for Managed Firewall Services ?

Expertise and Experience
Our team of penetration testers brings a wealth of knowledge and experience, having worked across various industries and technologies. They are well-versed in the latest cyber threat landscape and penetration testing methodologies.

Comprehensive Security Assessment
We offer a full spectrum of penetration testing services, including network penetration testing, application security testing, and wireless security testing. This comprehensive approach ensures no aspect of your cyber security is left unchecked.

Customized Testing Strategies
Understanding that every organization’s security needs are unique, we tailor our penetration testing strategies to align with your specific business objectives, regulatory requirements, and risk tolerance levels.

Actionable Insights and Remediation Support
Beyond identifying vulnerabilities, we provide detailed reporting on our findings, offering actionable insights and practical recommendations for remediation. Our team is also available to assist with implementing these security measures, ensuring your defenses are strengthened effectively.
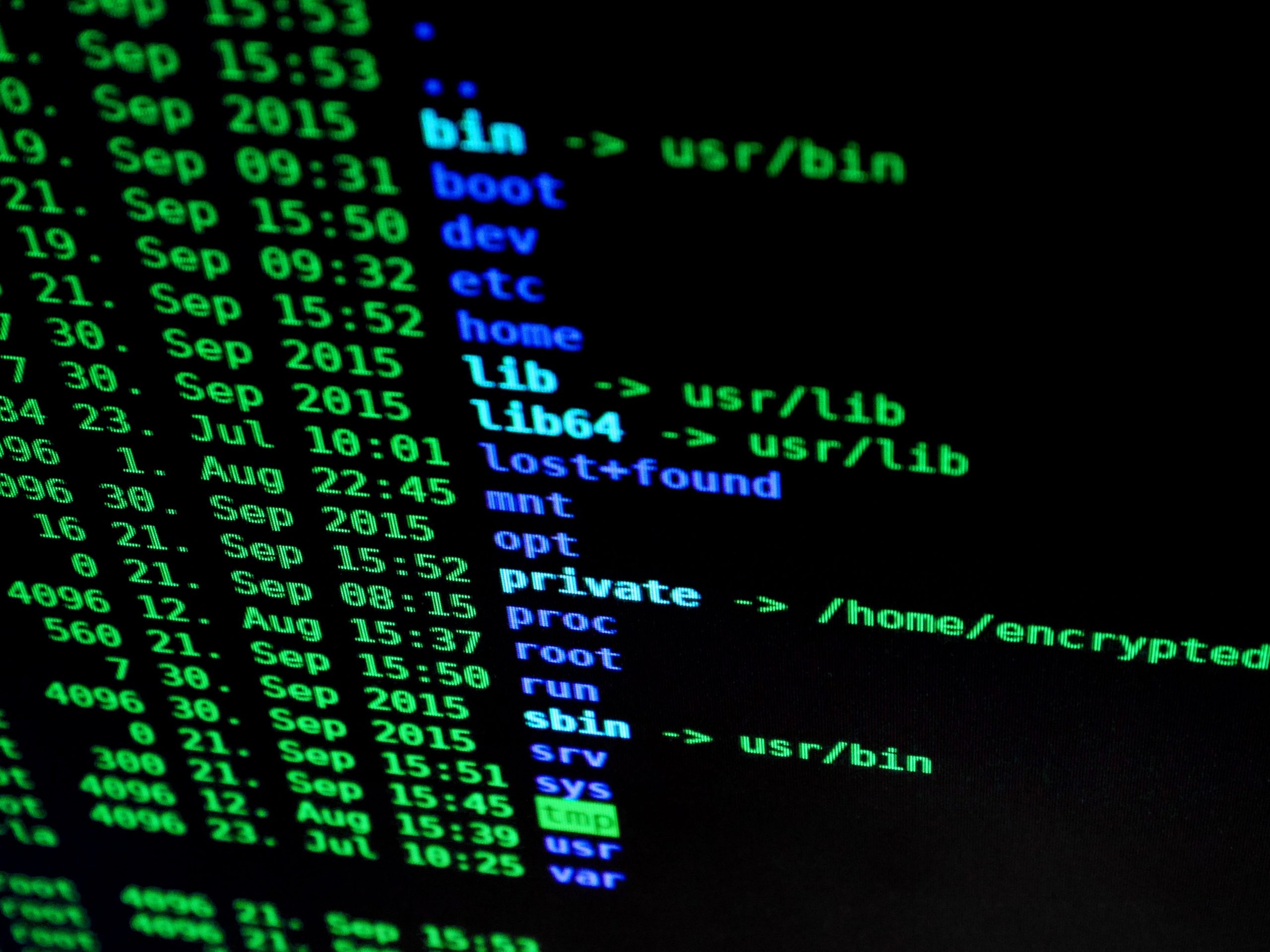
Elevate Your Cyber Security with TDR Networks
Penetration testing is an essential component of a proactive cyber security strategy. By identifying and addressing vulnerabilities before they can be exploited, you not only protect your organization from potential breaches but also reinforce your commitment to security to your clients, partners, and stakeholders.
With TDR Networks’ Penetration Testing Services, you gain a trusted partner dedicated to enhancing your cyber defenses. Our expertise, comprehensive testing methodologies, and commitment to actionable insights and remediation support ensure your organization is equipped to face the cyber threats of today and tomorrow.
Our Process
Simulating attacks to identify weaknesses, fortify systems – and enhance cybersecurity defenses.
Scoping and Planning/Intelligence Gathering
Vulnerability Analysis
Exploitation & Post-Exploitation and Analysis
Reporting and Debriefing & Remediation Support

1
Scoping and Planning/Intelligence Gathering
We begin with a thorough consultation to understand your environment, objectives, and specific concerns. This phase helps define the scope and objectives of the penetration test, ensuring it is aligned with your needs.
Our team collects information on the target environment to identify potential vulnerabilities and attack vectors. This reconnaissance is crucial for planning the penetration test.

2
Vulnerability Analysis
Using a combination of automated tools and manual techniques, we identify and assess vulnerabilities within the scoped environment.

3
Exploitation
We simulate controlled attacks to exploit identified vulnerabilities, determining their potential impact on your operations and data.
Post-Exploitation and Analysis
After successful exploitation, we explore the compromised system’s depth and breadth to understand the severity of each vulnerability.

4
Reporting and Debriefing
Our comprehensive report details the vulnerabilities discovered, the exploitation process, and recommendations for remediation. We also provide a debriefing session to discuss our findings and next steps.
Remediation Support
We offer guidance and support in addressing identified vulnerabilities, helping you strengthen your security posture against future attacks.
Best IT Solutions for your Business
Our team brings a wealth of practical experience and technical expertise. A track record of success and satisfied clients.
Find Us on Facebook, Instagram, Tiktok and LinkedIn

Years Experience

Projects

No. of Clients
Let's Connect Us?
Your IT challenges, solved.
Interested in elevating your IT infrastructure or curious about how we can drive your business forward? We're here to help. Get in touch with our team to discuss your needs or to simply ask a question. We're ready to provide you with the solutions you need and the support you deserve.
Reach Out Today:
Phone: 028 90 286150
Email: support@tdrnetworks.com
Office Hours:10am - 6pm
Or, fill out our quick Contact form and we'll get back to you promptly.